Ground Reports
Explained: Chinese Hackers Targeted Power Grid Near Ladakh; Government Says It Monitored, Foiled Attempts
Swarajya Staff
Apr 08, 2022, 02:46 PM | Updated Apr 10, 2022, 07:12 AM IST
Save & read from anywhere!
Bookmark stories for easy access on any device or the Swarajya app.
Chinese state-sponsored hackers tried to hit Indian power grid assets near Ladakh, where the two countries have been locked in a stand-off since May 2020, a report by Recorded Future, a cybersecurity company based in Massachusetts, US, has revealed.
The Narendra Modi government has acknowledged the reports, with Power Minister R K Singh saying that his ministry was aware of the attempts by Chinese hackers to attack the Indian power grid and that these were foiled by the mechanisms put in place by India over the last few years.
Recorded Future Report
In its report, Recorded Future has said that the attacks on the Indian power grid have been "geographically concentrated" in the northern parts of the country, adding that the assets which were targeted were located "in proximity to the disputed India-China border in Ladakh."
The report, which is available here, says that Recorded Future has found at least seven "network intrusions targeting at least seven Indian State Load Despatch Centres (SLDCs) responsible for carrying out real-time operations for grid control and electricity dispatch".
"To achieve this, the group likely compromised and co-opted internet-facing DVR/IP camera devices," the report says.
The report says that the Chinese hackers may have been conducting "pre-positioning activity", which means the placement of malware within the electrical grid without activation. Experts believe pre-positioning could either be a signal to India or a preparation for a larger attack on the Indian power grid in the area. In the latter case, the malware can be activated at a later stage, when the hackers want to cause disruption in supply.
With such intrusions through state-sponsored hackers, China may be trying to gain a better understanding of the system, which would help its hacking army develop capability for "future use" and may also give them access needed to prepare for "future contingency operations".
The repeated attacks on India's power grid assets by the Chinese provide them "limited economic espionage or traditional intelligence-gathering opportunities", the report says, adding, "we believe this targeting is instead likely intended to enable information gathering surrounding critical infrastructure or is pre-positioning for future activity."
Government Knew About The Attacks, Says Power Minister
Power Minister Singh has said the government knew about the "attempts at hacking" which have been reported by Recorded Future.
Singh revealed that the Chinese hacking attempts were made in January and February this year and were unsuccessful due to the measures India has taken over the last few years to improve cyber security.
"What it is talking about, that report, refers to attempts at hacking which happened in January and February, not now. Those attempts were already reported to us. We had a meeting with the concerned states and reviewed the situation," the Power Minister has told the media.
"I must tell you that we have been conscious about the need for strengthening our cyber security mechanisms. We have strengthened them and we review it constantly," he said, adding, "There were attempts at cyber attacks but those attacks have not succeeded."
"I would call them probing attempts, to try and see if there is any vulnerability. We have put in place systems to stop it," the minister said.
MEA Reacts, China Denies
The Ministry of External Affairs (MEA) has also reacted to the development.
"We have seen the reports. There is a mechanism in place so that our critical infrastructure remains resilient in such cases... We have systems in place to safeguard critical infrastructure," Arindam Bagchi, spokesperson of the Ministry of External Affairs, said.
When asked if India had raised the issue with China, Bagchi said, "I don't have any information that we have raised the issue with China."
In Beijing, Foreign Ministry spokesperson Zhao Lijian said China had nothing to do with the attacks on the Indian power grid reported by Recorded Future.
"I noted relevant reports. We have reiterated many times that China firmly opposes and combats all forms of cyber attacks in accordance with law...Given the virtual nature of cyberspace and the fact that there are all kinds of online actors who are difficult to trace, it's important to have complete and sufficient evidence when investigating and identifying cyber-related incidents. One should be all the more prudent when associating cyberattacks with the government of a certain country," he said at the daily press briefing on 7 April in response to a question from Bloomberg.
Pointing the finger at the US, he called the country "the world's largest source of cyber attacks" and labelled it as the "hacking empire".
He also attacked Recorded Future, which monitors Chinese state-sponsored cyber attacks closely, saying, "if they really care about global cyber security, they should pay more attention to the cyber attacks by the US government-sponsored hackers on China... and do more to promote dialogue and cooperation among countries, rather than sow discord and sling mud at China under the pretext of cyberattack issues."
Not The First Chinese Attack On Indian Power Grid Amid Tensions
In 2021, Recorded Future had reported that Chinese state-sponsored groups could have been behind the electricity blackout in Mumbai in October 2020, just months into the stand-off between India and China in eastern Ladakh.
It had noted that a "concerted campaign" was launched against large swathes of India's power sector, targeting at least 10 Indian power sector organisations, including four of the five Regional Load Despatch Centres in the country responsible for the integrated operation of India's power grid, including balancing electricity supply and demand to maintain a stable grid frequency.
The Recorded Future report has identified RedEcho as the Chinese state-backed group behind the attack on India's power grid, including high-voltage transmission substation and a coal-fired thermal power plant.
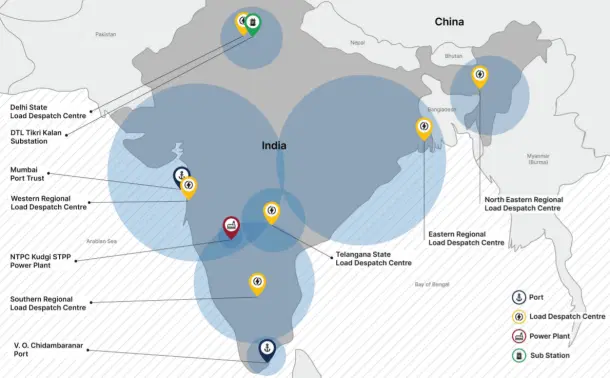
"In total, we identified 21 IP addresses resolving to 10 distinct Indian organizations in the power generation and transmission sector that were targeted," the report by Recorded Future says.
Recorded Future was able to track targeted attacks against 12 Indian entities, all of which qualify as critical infrastructure according to the National Critical Information Infrastructure Protection Centre definition.
Apart from the power grid, targets include Mumbai and Tuticorin ports.
India May Have Responded In Kind
Interestingly, in its report on the Chinese link to the Mumbai blackout, Recorded Future had also stated that it had observed attacks against the Chinese military and government entities by "suspected Indian state-sponsored group Sidewinder" in 2020, hinting that New Delhi may have been responding to Chinese provocations on the cybersecurity front to deter Beijing.
In October 2021, Global Times, a jingoistic subsidiary of the Chinese Communist Party mouthpiece People's Daily, has also accused India of targeting China's defence and military departments with cyber attacks.
"...hackers from India behind the attempts to launch attacks on China's defense and military units as well as state-owned enterprises," claimed the Global Times report, which was based on the findings of Antiy Labs, a "leading anti-virus company" in China.
This activity, it added, was "mainly targeted the country's government, defense and military units, as well as state-owned enterprises in China, Pakistan, and Nepal."
"The hackers disguise themselves as government or military personnel and deliver emails with phishing attachments or embedded links to targets luring them to visit the websites created by them and collect the account password for intelligence gathering," Amity Labs told Global Times.